WithSecure™ Playground
Discover, grow, and retain cyber security talent to defend against modern attackers
Playground encourages hands-on problem solving and experimentation within security, IT, and tech teams.
Users can test and improve their technical knowledge practically, in a lifelike but safe environment. Playground continues to be developed and used by our own consultants and developers: specialists on the frontline of cyber security.
What are the features?
This course uses step-by-step tutorials and practical exercises to give participants working knowledge of mobile hacking on iOS and Android. Understanding the basic principles of vulnerability hunting on-platform, all the way through to advanced exploitation techniques, will equip you to develop secure and resilient mobile apps for your organization or clients.
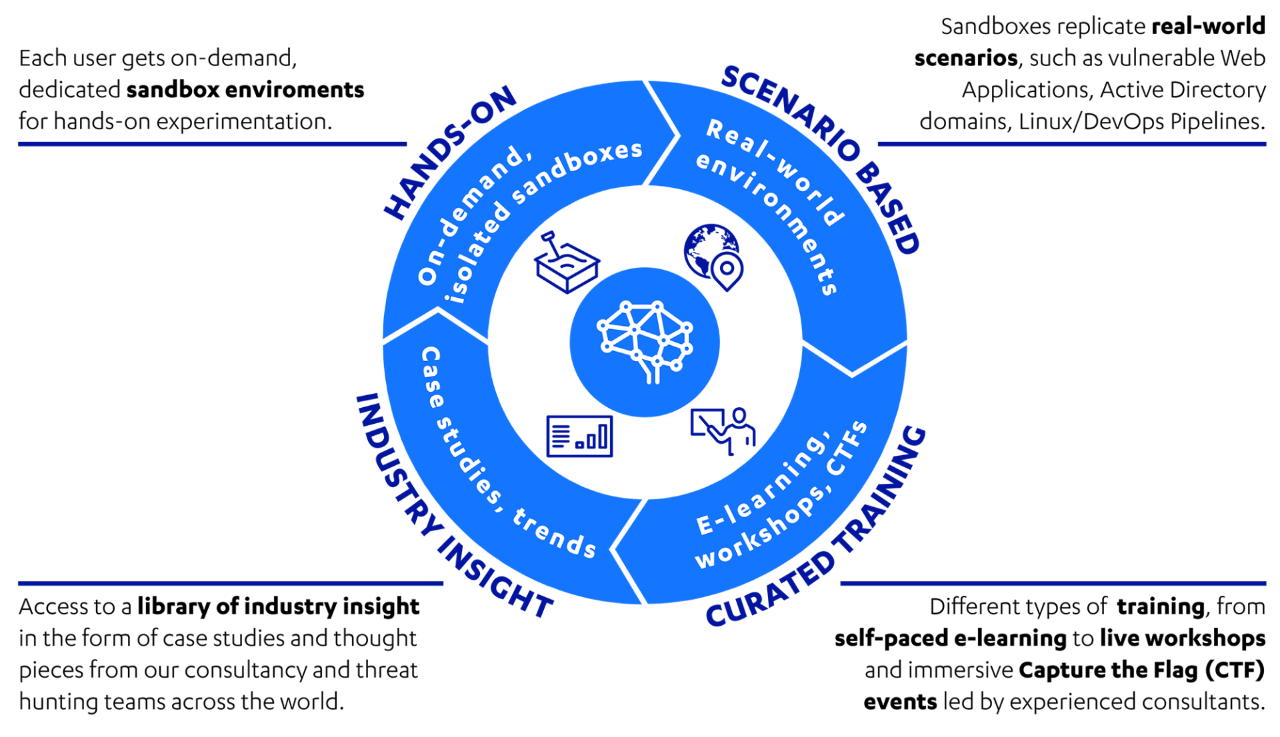
Hands-on
On-demand, dedicated sandboxed training environments to develop and exercise cyber security skills.
Scenario-based
Improve outcomes by engaging participants in relevant, real-world scenarios.
Curated training
Holistic training, including guided learning, CTFs, hackathons, bespoke consultancy, and ”build your own” content.
Industry insight
Content curated by industry experts who understand modern attacks and effective defense.
WithSecure™ Playground methodology
Reporting
The reporting features allow you to keep track of users’ progress and engagement. User-friendly dashboards enable you to spot talent in your team and reward it. Rich data shows you exactly where members of your team are excelling and where they need support—this enables knowledge gaps to be identified quickly and resolved with suitable training.

Playground learning pathways
Playground training content is organized into learning pathways. Users can progress through different levels of our standard pathways, developing confidence and competence along the way.
Our standard pathways include application security, attack detection, and penetration testing. Custom pathways can be designed for specific needs.
Select learning pathways for more information
Vulnerabilities in applications, especially web applications, have consistently accounted for most data breaches. It is essential for organizations to equip their software developers and DevOps engineers with the skills and knowledge to integrate security into their SDLC (Software Development Lifecycle). This will allow them to build robust and secure applications that can withstand modern attackers.
Application Security
Users: software developers and DevOps personnel
The root of security issues can always be traced back to how software has been designed and developed. This pathway raises awareness of the impact of insecure development practices. It drives security expertise within the development team, so that most security issues can be built out earlier in the product lifecycle or quickly.
Organizations are increasingly looking to invest in security monitoring and threat detection. Ensuring personnel have the skills and knowledge to identify and respond to malicious activity is essential to effective attack detection.
Pentesting
Organizations with a strong security posture are investing in their internal pentesting capability. Developing and retaining skilled personnel in this area can be challenging, but this can be addressed by exposing teams to how the most advanced attackers think and act in the wild.
Attack & Detection
Software developers and DevOps engineers: pentesters, red teamers, security operations, SOC analysts, and threat hunters
The initial pathway levels start with a focus on attack detection and pentesting respectively, to then merge into one advanced level which provides access to all training labs used by WithSecure consultants—including the exclusive advanced labs used at WithSecure yearly hacking competition HackFu.
Get started now
1
Fill the form
Fill in the form below to contact us for more details.
2
We'll be in touch
We will reach out to you in a few days to make sure that you've had a smooth start and to help with any questions or concerns.
3
Boost your security with a dedicated partner
We will support you to help you get the most out of WithSecure Product Consulting and Training service.
Want to talk in more detail?
Complete the form, and we'll be in touch as soon as possible.