Cloud Security Posture Management
Cloud service configuration assurance with unmetered access to cloud configuration expertise that helps you prioritize findings and take actionable steps to fix insecure configurations of AWS and Azure services.

Most enterprises operate hybrid, multi-cloud networks which are complicated to defend.
Misconfiguration is the leading cause of data breaches and according to our own research, it is the most common source of major cloud security incidents.
Gartner predicts that “through 2025, 90% of the organizations that fail to control public cloud use will inappropriately share sensitive data.”
Cloud vendors have developed tools to spot misconfigurations, but to be effective, they must be configured and managed by someone skilled and capable of interpreting their outputs. These skills are scarce. How can organizations ensure that they have effective controls to secure the cloud?
WithSecure’s Cloud Security Posture Management (CSPM) service performs the configuration checks necessary to assure security, and communicates the results and recommendations to you in an actionable form.
What can you achieve?
Security engineering partnership
Help you assess the impact of misconfigurations and to implement secure configurations
Deterrence value
In the form of on-going security improvements that make your organisation less attractive to attackers
Assurance to auditors and regulators
Adequate cloud security risk and governance controls

Our approach
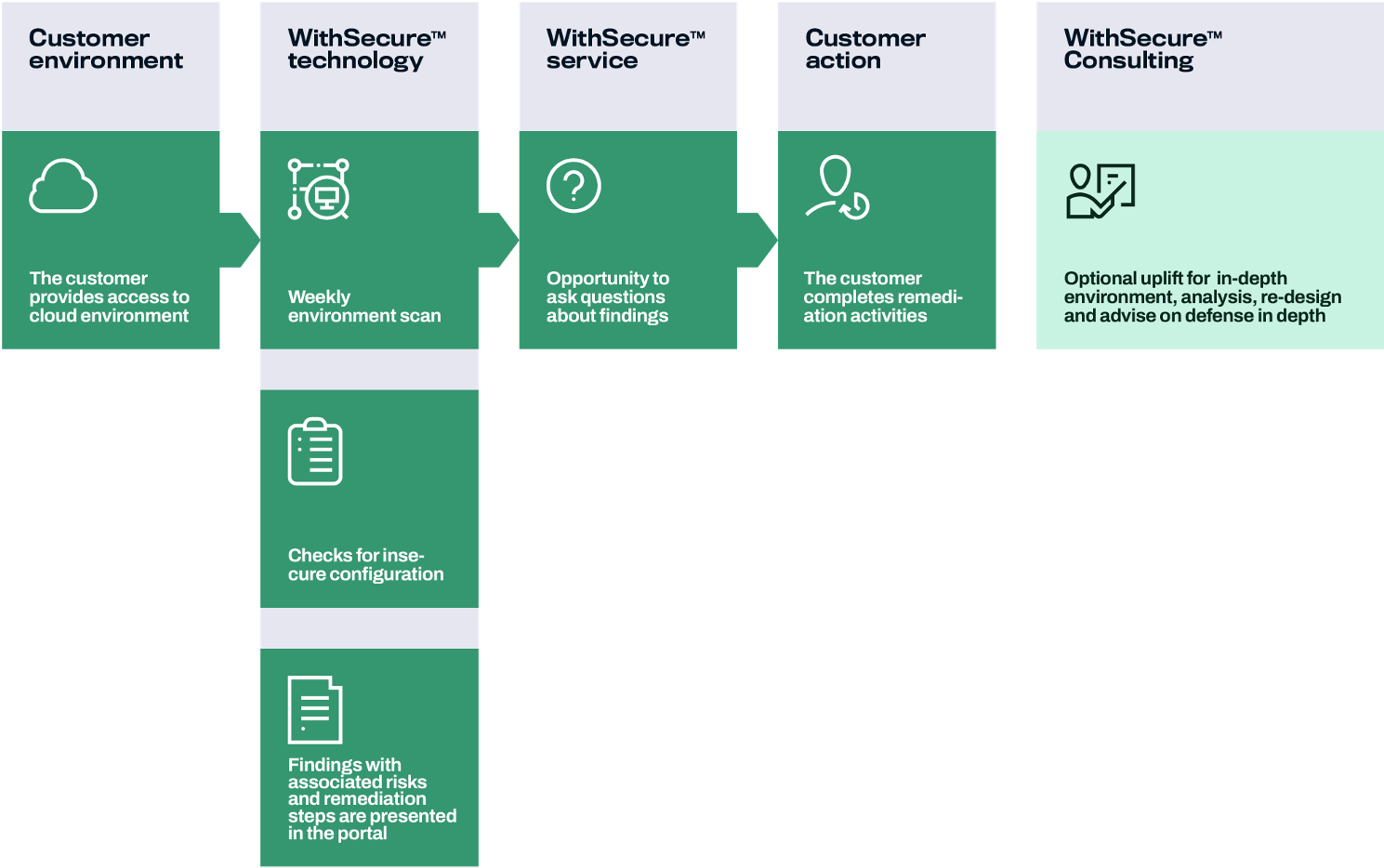
CSPM solutions on the market come in a bewildering range of flavours. The majority are easy-to-implement SaaS solutions, but they require somebody with a PhD to understand their outputs and make sensible security decisions. At WithSecure, we believe that organisations can best manage their security posture by using a service that combines high-quality people with our own purpose-built technology. Three pillars define our CSPM service:
- Security through partnership: we appoint a Security Engineer who understands your environment to assist your understanding of misconfigurations and their impact and to help you assess your cloud security risk. This goes far beyond what a product can offer.
- Unmetered access to cloud configuration expertise: WithSecure Security Engineers will help you prioritize findings and provide actionable steps to fix insecure configurations and address your cloud configuration management queries.
- Compliance assurance through out-of-the-box cloud security checks: we employ an algorithm developed by WithSecurity Consultants that specialize in securing cloud environment to check for misconfigurations. The checks go beyond industry standards and benchmarks as they have been shaped by experience on the front line. Our service is continuously improved to account for changing standards, new attack methods and evolution of the underlying cloud platform.
The evidence provided by the tool can be used to demonstrate how your organization aligns to cyber security frameworks and standards.
Key features of our service
- Monthly scan of AWS and Azure cloud environments and a report
- Monthly re-scan upon request
- Monthly meeting with dedicated Security Engineer and access for queries during working hours
- Continuous improvement to existing checks and addition of new ones
- Optional consulting support for analysis and remediation.
Speak to the team
Want to significantly reduce the risk posed by your external perimeter? We can help.
Related resources
The Microsoft Azure Security Framework
Inspired by Scott Piper's roadmap for building cloud security in AWS, our MS Azure security framework provides the building blocks required to harden your Azure platform from the ground up.
Read moreEffective detection and response in a cloud service world
200 years ago, every factory had its own power source: a steam engine or a waterwheel, yet few businesses today generate their own power. They buy electricity, instead.
Read moreHow cloud security posture management will help you
Over 90% of enterprises have a hybrid, multi-cloud strategy.
Read more- Slide 1
How WithSecure™ can help?
Cloud services are easy to misconfigure, exposing enterprises to attack. Misconfiguration is the most common cause of the largest breaches of cloud services to date, which is why we now have cloud security best practices and standards.
Cyber security based on compliance to rules or standards may make it easier to get through audits, but they it does not make you secure. The CSPM checks we perform are based on the CIS Foundational Framework and the AWS Security Best Practices checks, favored by auditors. They are supplemented by over 30 checks that WithSecure believes are necessary, based on our front line experience of combatting cyber attacks.
Want to talk in more detail?
Complete the form, and we'll be in touch as soon as possible.